Tamper
/ˈtæm.pɚ/: to touch or make changes to something that you should not, usually without enough knowledge of how it works or when you are trying to damage it:
I could see immediately that the lock had been tampered with.
Tampering with pipelines could result in ruptures or fires.
Poll workers are trained to recognize signs of machines that had been tampered with.
to speak to and try to influence someone involved in a legal case:
She is charged with official misconduct and tampering with witnesses.
A previous trial was stopped owing to fears of someone tampering with the jury.
====================
Can you tamper with JWT tokens?
The header and payload of signed tokens are protected against tampering, but the data contained in the JWT can be changed without modifying the signature.Dec 26, 2022
How does JWT prevent tampering?
When a client receives the JWT, it can verify the Signature using the shared secret or public key associated with the issuer. Any unauthorised changes to the token's content or tampering with the Signature will be detected, rendering the token invalid.
Can JWT be intercepted?
Also, while the security risks are minimized by sending JWTs using HTTPS, there is always the possibility that it's intercepted and the data deciphered, exposing your user's data. Remember, JWTs can be seen by anyone who intercepts the token because it's serialized, not encrypted.
=======================
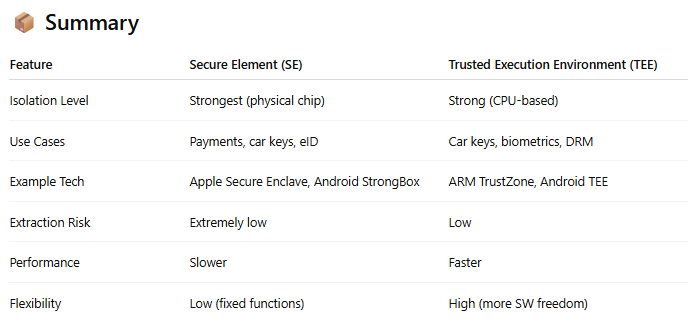
🔐 "Store in Secure Element or TEE" — What It Means
When we say store digital keys in a Secure Element (SE) or Trusted Execution Environment (TEE), we mean placing sensitive data (like vehicle access credentials) in isolated, hardware-backed environments that are resistant to attacks — even if the main phone OS is compromised.
🔒 1. Secure Element (SE)
A tamper-resistant chip embedded in the smartphone or wearable.
Stores and processes sensitive data independently from the main OS (Android/iOS).
Similar to what's used in credit cards, SIM cards, or payment systems (e.g., Apple Pay).
Supports hardware-based encryption, key generation, and secure communication.
📌 Used by: Apple Wallet, Samsung Knox Vault, Android StrongBox (Pixel phones)
🧠 2. Trusted Execution Environment (TEE)
A secure zone inside the main processor, isolated from the rest of the OS.
Runs a trusted OS (e.g., ARM TrustZone) in parallel with Android/iOS.
Supports secure key management, digital signing, decryption, etc.
Less secure than SE, but more flexible and still hardened.
📌 Used by: Android Keystore (TEE-backed), some banking apps, digital key apps
✅ Why Use SE or TEE for Digital Keys?
Because BLE/UWB digital keys can control vehicle lock, start, or summon — you must prevent:
Key extraction by malware/rootkits
Key replay or tampering
OS-level spoofing
Without SE/TEE:
A rooted phone or compromised app could read and reuse your key material.
With SE/TEE:
Even with full system compromise, the keys cannot be read, copied, or tampered with — because all sensitive operations stay inside the protected environment.
"Tamper" means to interfere with something in an unauthorized or harmful way, usually with the intent to alter, damage, or bypass it.
🔧 In Automotive or Security Context:
Tampering refers to any unauthorized access, modification, or disruption of a system or component.
🔐 Examples:
Tampering with a digital key: Extracting or modifying the key stored in a smartphone to gain unauthorized access to a vehicle.
Tampering with ECU firmware: Hacking into the vehicle control software to disable safety limits or change behavior.
Tampering with sensor data: Injecting fake signals or modifying real ones to mislead the vehicle (e.g., making it think the road is clear when it’s not).
💥 Why Tampering Is Dangerous
It bypasses safety and security protections
It may lead to theft, malfunction, or even accidents
It often violates compliance (e.g., ISO 26262 or ISO/SAE 21434)
🛡️ How Tamper Protection Is Achieved:
Tamper-evident hardware (seals, enclosures)
Cryptographic checks (digital signatures, secure boot)
Secure storage (SE/TEE or HSM)
Intrusion detection (voltage, temperature, physical access)
Let me know if you want real-world automotive examples or technical countermeasures.